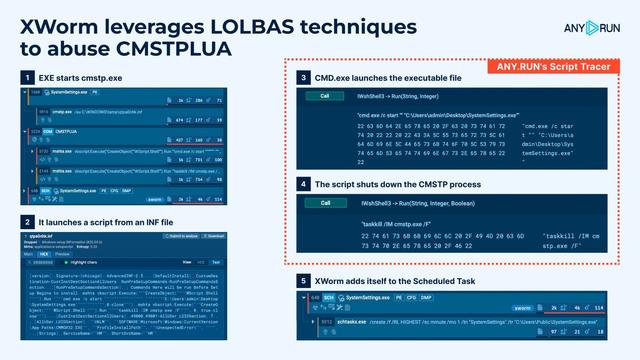
#XWorm leverages LOLBAS techniques to abuse #CMSTPLUA
CMSTPLUA is a legitimate Windows tool that can be exploited for system binary proxy execution using #LOLBAS techniques, bypassing security controls like #UAC, and executing #malicious code, putting organizations at risk.
With Script Tracer in #ANYRUN Sandbox, a SOC team can analyze scripts more efficiently. It simplifies script breakdowns, making it easier to understand their behavior and get key insights.
The #script embedded in the INF file is used to coordinate an execution chain: EXE starts cmstp.exe which is used to launch a #malicious script from an #INF file.
CMSTPLUA
mshta.exe
cmd.exe
EXE
PowerShell
– #MSHTA loads a #VBScript from memory to run an executable and shuts down the #CMSTP process.
– EXE launches #PowerShell to add itself to #MicrosoftDefender exceptions.
Finally, it runs the XWorm #payload from the #System32 directory and adds itself to the Scheduled Task for persistence.
Check out the analysis and see Script Tracer in action:
https://app.any.run/tasks/9352d612-8eaa-4fac-8980-9bee27b96bce/?utm_source=mastodon&utm_medium=post&utm_campaign=cmstplua&utm_term=130225&utm_content=linktoservice
Living-off-the-Land techniques have been leveraged for years to execute malicious operations using legitimate system utilities.
Use these TI Lookup search queries to find similar samples and improve the efficiency of your organization's security response: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=cmstplua&utm_content=linktoti&utm_term=130225#%7B%2522query%2522:%2522commandLine:%255C%2522%255C%255C.inf%255C%2522%2520AND%2520imagePath:%255C%2522cmstp%255C%255C.exe$%255C%2522%2522,%2522dateRange%2522:180%7D
https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=cmstplua&utm_content=linktoti&utm_term=130225#%7B%2522query%2522:%2522commandLine:%255C%2522mshta%2520vbscript:%255C%2522%2522,%2522dateRange%2522:180%7D